This article is for technical system administrators who can access your organisation's identity management system
This article explains how to set up and configure single sign-on between Checkbox and your Azure Active Directory or ADFS.
Create the SAML Enterprise Application
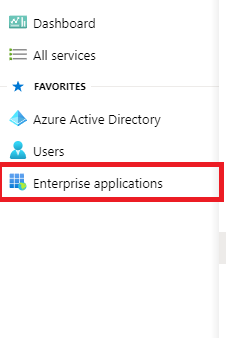
- Go to your Azure admin center - https://aad.portal.azure.com/
- Click on 'Enterprise applications'
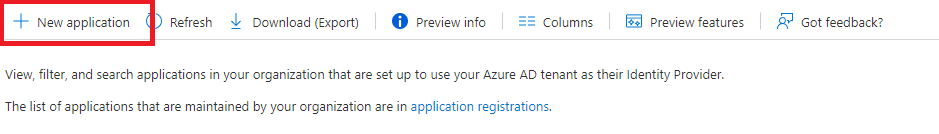
- Click on 'New application'
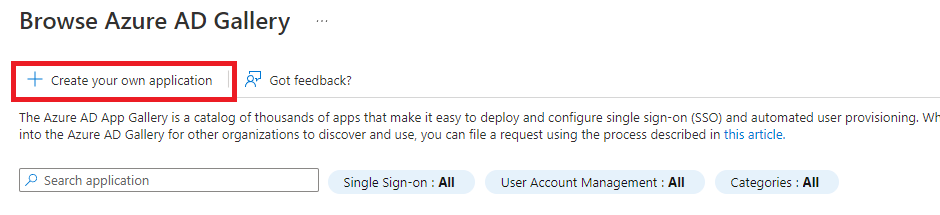
- Click 'Create your own application'
- Give this Application a name and select the 'Integrate any other application you don't find in the gallery'
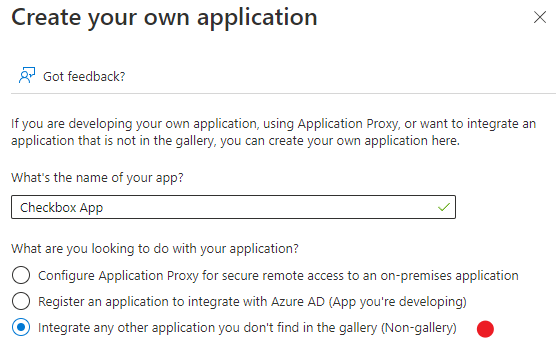
- Press 'Create'
Configure your Application with Checkbox SAML Details
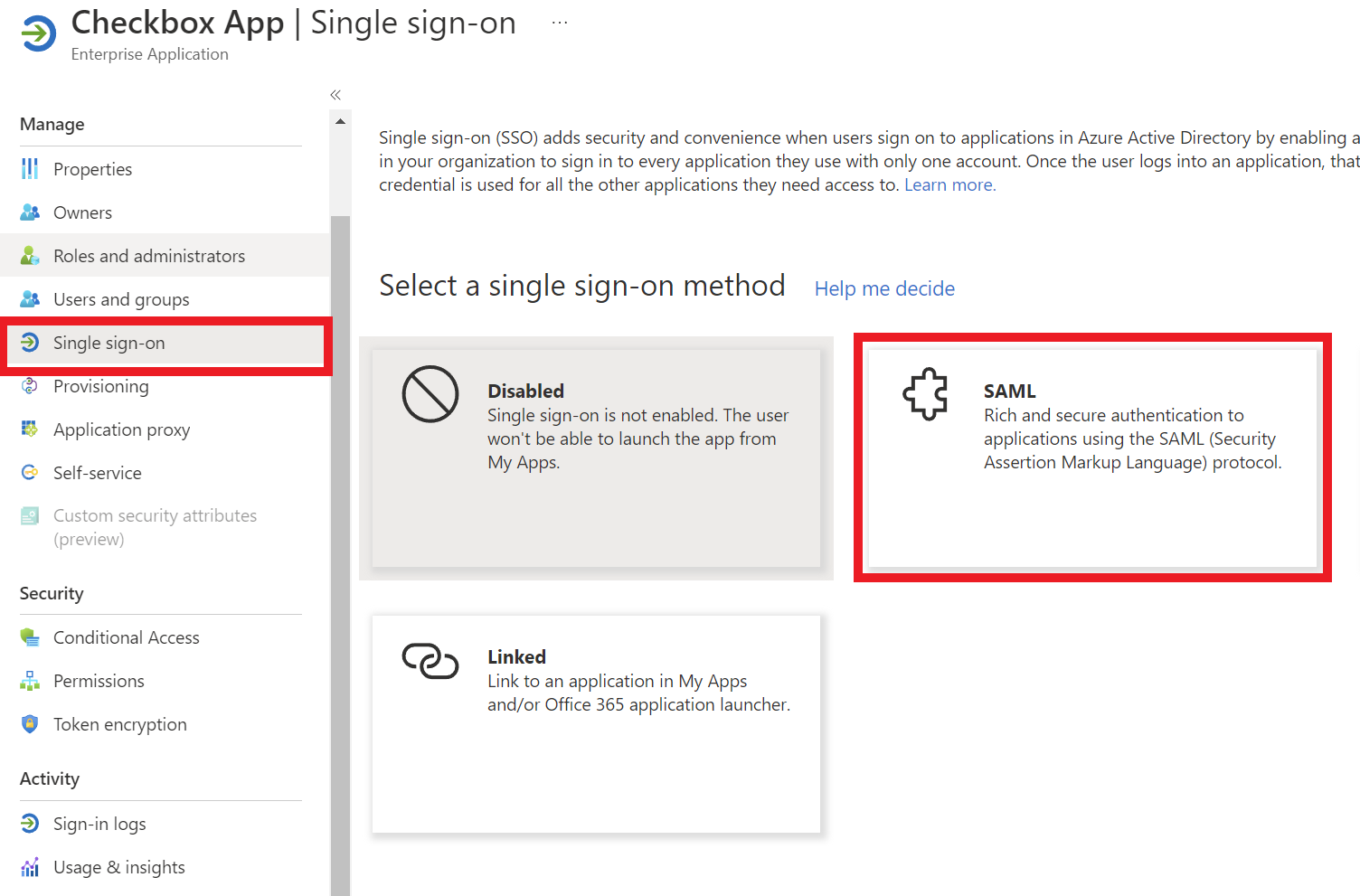
- Once your Application has been created, click 'Set up single sign on' from your new Application's Dashboard and select 'SAML'.
- Click on 'Edit' for Basic SAML Configuration

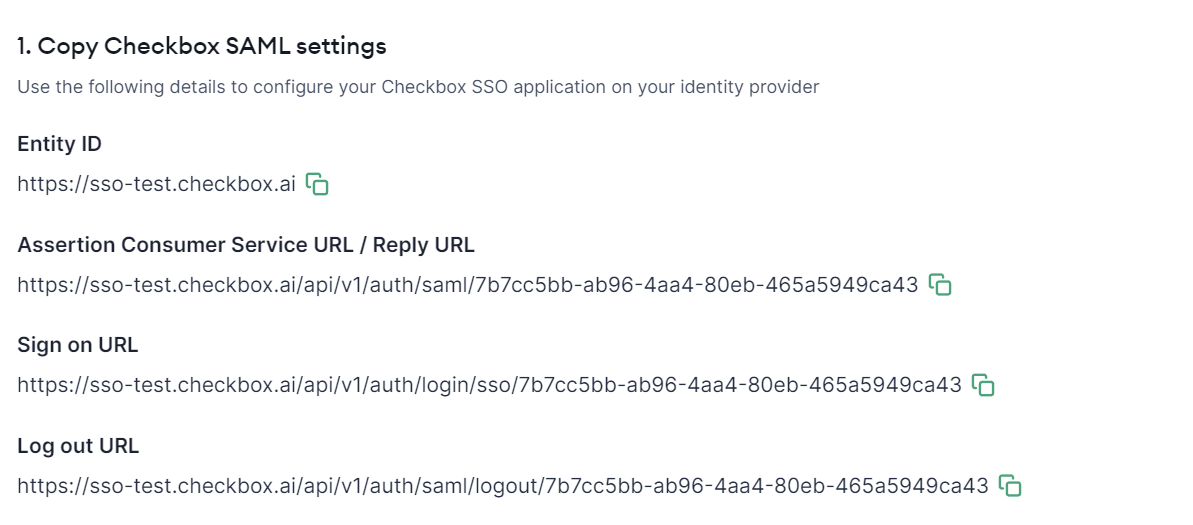
- On Checkbox, go into Account Settings > SSO Configuration and copy the details from 'Step 1: Copy Checkbox SAML Settings' of the self-serve guide over into the corresponding fields in your Azure Application's Basic SAML Configuration settings.
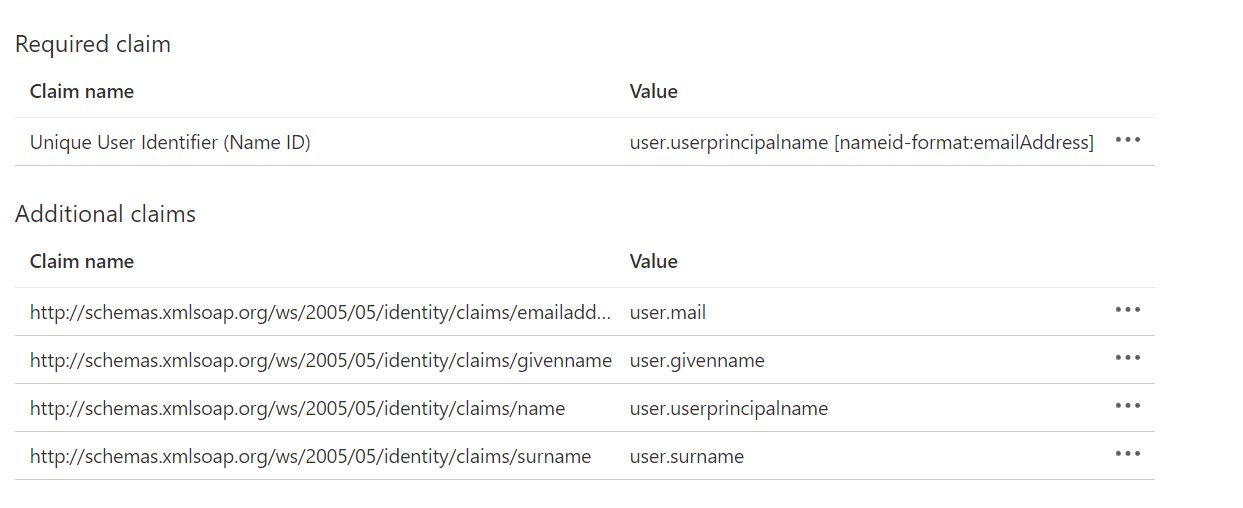
- On Azure, continue on to configure the 'Attributes & Claims' section, and ensure your claims match the following.
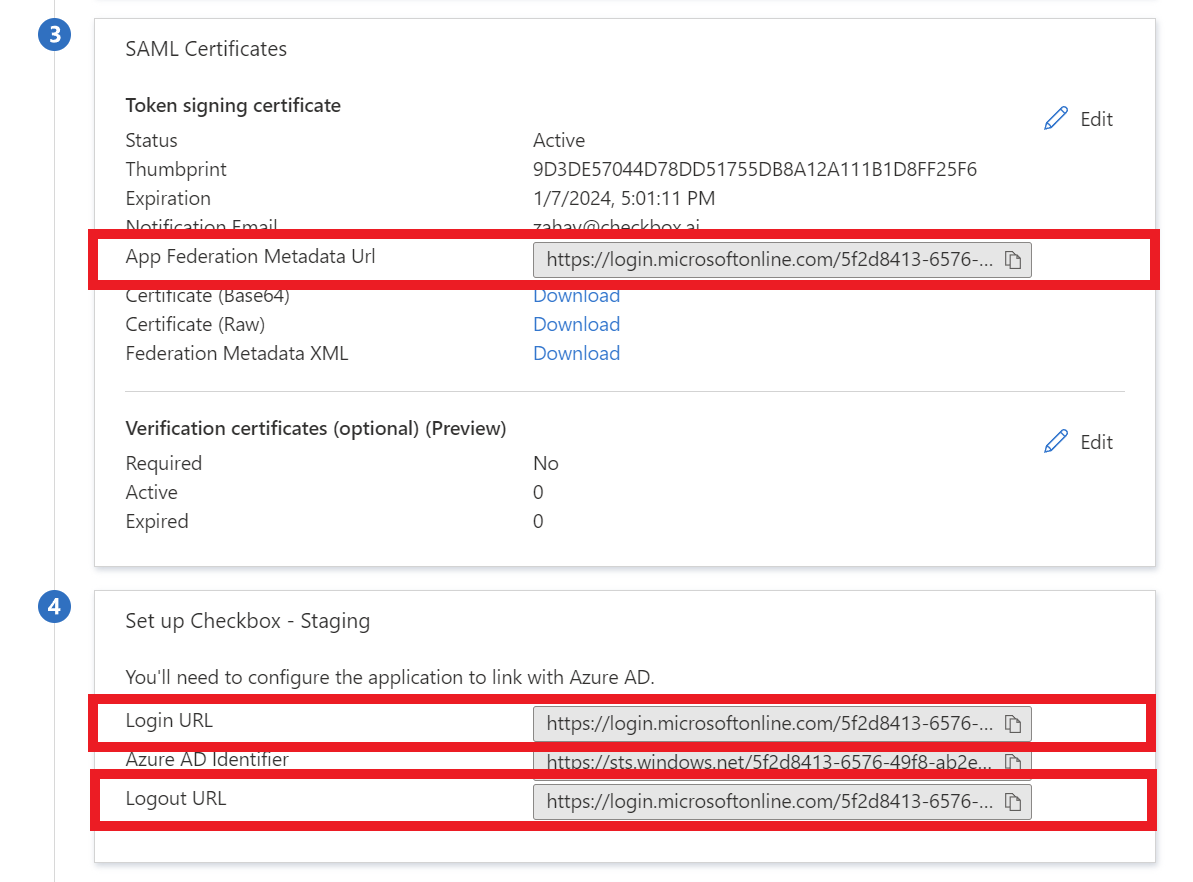
- On Azure, find your App Federation Metadata URL, Login URL and Logout URL, and copy these details into the Metadata URL, Sign on Endpoint, and Sign off endpoint fields on Checkbox respectively.
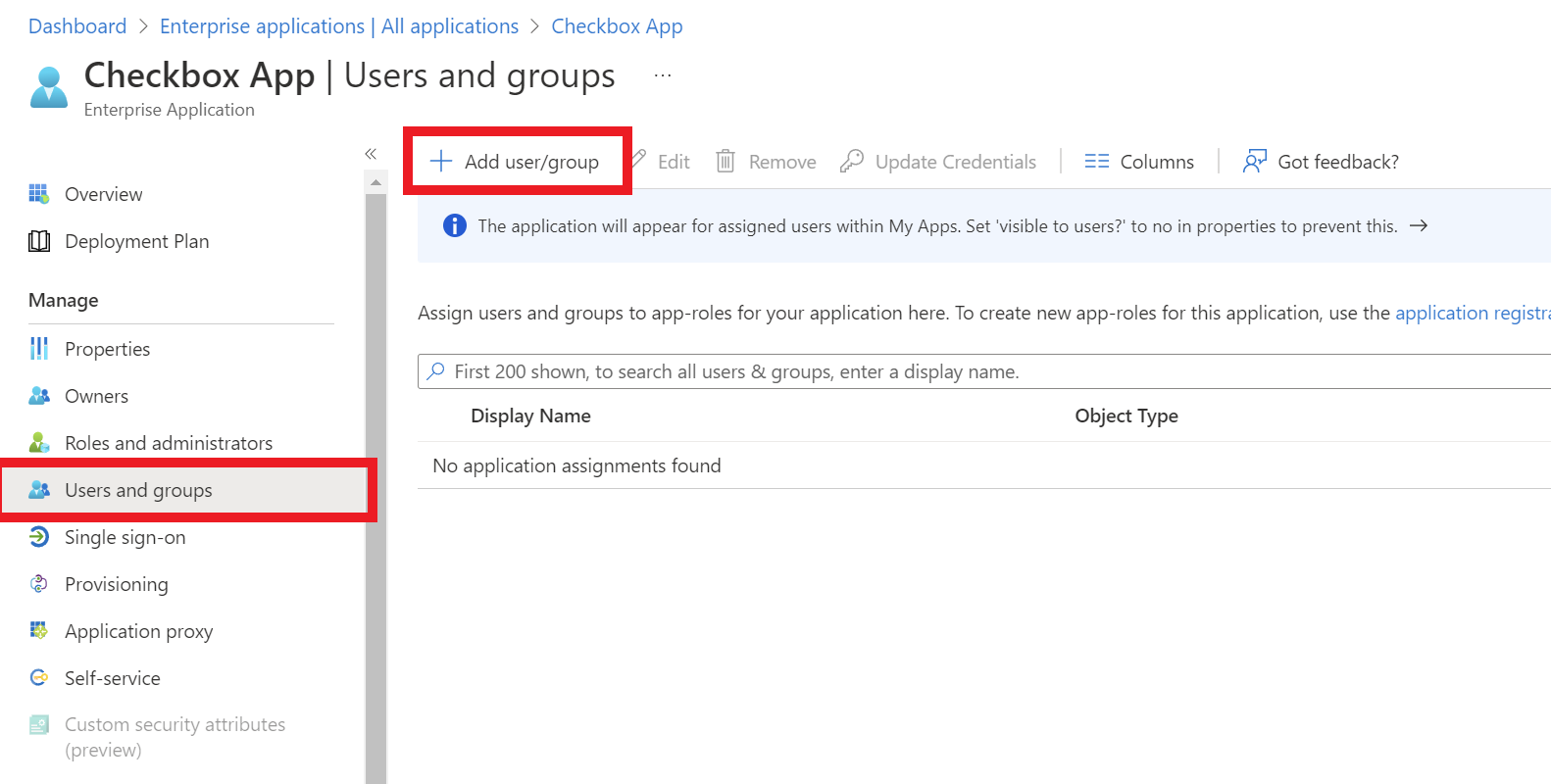
Provision user access
On Azure, click on 'Users and Groups' and click Add user/group to provision access to Checkbox via Azure.
Test your SSO Connection
Once you configured your SAML Application settings and assigned users or groups to Checkbox, you can now test your SSO connection. On Checkbox, go to step 4. Test Connection of the SSO configuration menu and click Test SSO Connection.
If everything has been configured correctly, you should be presented with a success message. If you had an error, please double-check your settings above, or contact our support team.
Once you have successfully configured and tested your SSO connection, you can enforce SSO for all users or just those users that match the registered domains.